|
1 | 1 | # misp-galaxy |
2 | 2 |
|
| 3 | + |
3 | 4 |  |
4 | 5 |
|
5 | 6 | 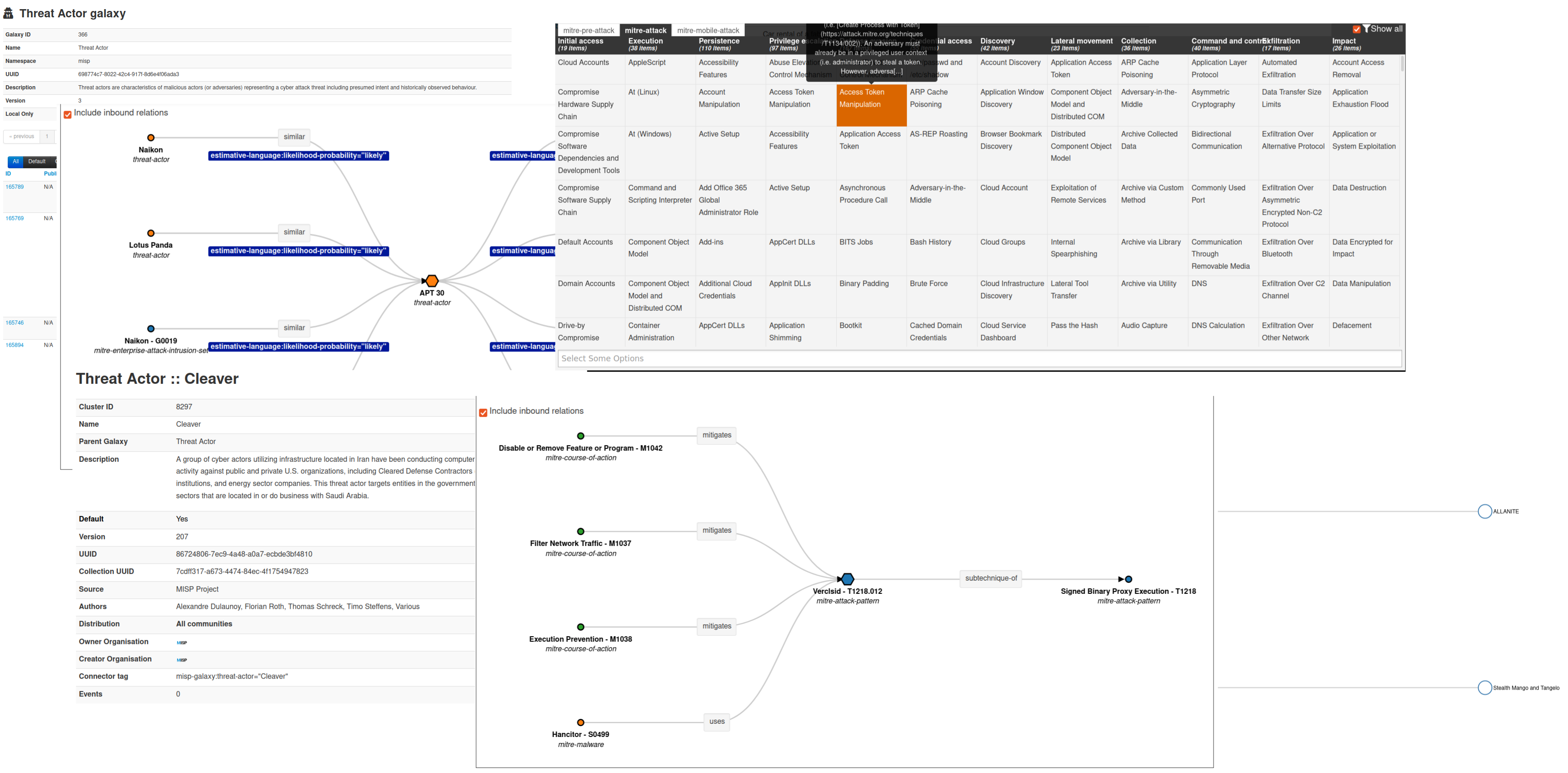 |
@@ -199,7 +200,7 @@ Category: *actor* - source: *MISP Project* - total: *4* elements |
199 | 200 |
|
200 | 201 | [Exploit-Kit](https://www.misp-galaxy.org/exploit-kit) - Exploit-Kit is an enumeration of some exploitation kits used by adversaries. The list includes document, browser and router exploit kits.It's not meant to be totally exhaustive but aim at covering the most seen in the past 5 years |
201 | 202 |
|
202 | | -Category: *tool* - source: *MISP Project* - total: *52* elements |
| 203 | +Category: *tool* - source: *MISP Project* - total: *53* elements |
203 | 204 |
|
204 | 205 | [[HTML](https://www.misp-galaxy.org/exploit-kit)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/exploit-kit.json)] |
205 | 206 |
|
@@ -707,11 +708,19 @@ Category: *tea-matrix* - source: ** - total: *7* elements |
707 | 708 |
|
708 | 709 | [[HTML](https://www.misp-galaxy.org/tea-matrix)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/tea-matrix.json)] |
709 | 710 |
|
| 711 | +## Canada Listed Terrorist Entities |
| 712 | + |
| 713 | +[Canada Listed Terrorist Entities](https://www.misp-galaxy.org/terrorist-groups) - Entities listed under Canada's Criminal Code as terrorist entities. |
| 714 | + |
| 715 | +Category: *threat-actor* - source: *https://www.publicsafety.gc.ca/cnt/_xml/lstd-ntts-eng.xml* - total: *90* elements |
| 716 | + |
| 717 | +[[HTML](https://www.misp-galaxy.org/terrorist-groups)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/terrorist-groups.json)] |
| 718 | + |
710 | 719 | ## Threat Actor |
711 | 720 |
|
712 | 721 | [Threat Actor](https://www.misp-galaxy.org/threat-actor) - Known or estimated adversary groups targeting organizations and employees. Adversary groups are regularly confused with their initial operation or campaign. threat-actor-classification meta can be used to clarify the understanding of the threat-actor if also considered as operation, campaign or activity group. |
713 | 722 |
|
714 | | -Category: *actor* - source: *MISP Project* - total: *941* elements |
| 723 | +Category: *actor* - source: *MISP Project* - total: *953* elements |
715 | 724 |
|
716 | 725 | [[HTML](https://www.misp-galaxy.org/threat-actor)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/threat-actor.json)] |
717 | 726 |
|
@@ -783,7 +792,7 @@ Category: *tool* - source: *MISP Project* - total: *606* elements |
783 | 792 |
|
784 | 793 | [UAVs/UCAVs](https://www.misp-galaxy.org/uavs) - OSINT Database of Unmanned Combat Aerial Vehicle |
785 | 794 |
|
786 | | -Category: *Military equipment* - source: *OSINT* - total: *661* elements |
| 795 | +Category: *Military equipment* - source: *OSINT* - total: *663* elements |
787 | 796 |
|
788 | 797 | [[HTML](https://www.misp-galaxy.org/uavs)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/uavs.json)] |
789 | 798 |
|
|
0 commit comments