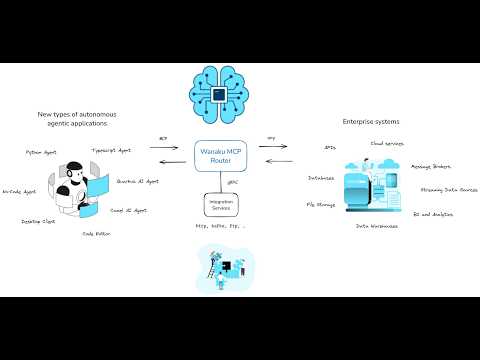
Wanaku aims to provide unified access, routing and resource management capabilities for your organization and your AI Agents.
The Wanaku MCP Router is an integration service designed to securely connect AI agents with various enterprise systems and cloud services. It acts as a central hub that manages and governs how agents access specific resources and tools, effectively proxying and filtering capabilities exposed to Large Language Models (LLMs).
The Wanaku MCP Router itself does not directly host tools or resources; instead, it acts as an integration service that connects AI agents with external resources and tools, including enterprise systems and cloud services. It manages and governs access between agent types and specific resources, proxying and filtering available capabilities to agents and their LLM
Wanaku provides specialized services, referred to as "capabilities" that offer specific functionalities to the Wanaku MCP Router.
These capabilities enable communication with various systems, such as Kafka services, message brokers, cloud services (AWS, Azure, Google, etc.), databases and a wide range of enterprise systems, including Workday and Salesforce, without directly containing the tools or resources.
Furthermore, Wanaku features an MCP-to-MCP bridge, which allows it to act as a centralized gateway or proxy for other MCP servers that use HTTP as the transport mechanism. This capability enables Wanaku to aggregate and effectively "hide" multiple external MCP servers, simplifying management and increasing the overall functionality of a Wanaku instance. Wanaku is an open-source project and is licensed under Apache 2.0.
If you haven't seen it already, we recommend watching the Getting Started with Wanaku video that introduces the project, and introduces how it works.
Note
Also check the Getting Started from the demos repository.
Using Wanaku MCP Router involves three key actions:
- Adding tools or resources to the MCP router
- Forwarding other MCP servers via the MCP forwarder
- Adding new capabilities via downstream services
Adding tools and resources to the Wanaku MCP Router expands the functionality available to agents using Wanaku.
- MCP tools equip an agent with capabilities not inherently present in its native models.
- MCP resources, on the other hand, allow an AI agent to consume data—such as files or records—and inject additional information into its context.
Both tools and resources depend on capabilities that can be dynamically added to or removed from the Wanaku MCP Router. Once these capabilities are integrated, either through downstream services or by connecting to other MCP servers, users can then incorporate new tools and resources into Wanaku. These additions can then leverage the newly integrated capabilities to interact with enterprise systems and cloud services.
Wanaku can act as a central gateway or proxy to other MCP servers that use HTTP as the transport mechanism. This feature allows for a centralized endpoint to aggregate tools and resources provided by other MCP servers, making them accessible as if they were local to the Wanaku instance.
This refers to extending the router's functionality by integrating with various external systems.
Wanaku leverages Quarkus and Apache Camel to provide connectivity to a vast range of services and platforms. This allows users to create custom services to solve particular needs. These services can be implemented in any language that supports gRPC for communication with the Wanaku MCP Router.
Note
It is also possible to create and run services in Java and other languages, such as Go or Python, although the process is not entirely documented at the moment.
Security in Wanaku involves controlling access to the management APIs and web interface while ensuring that only authorized users can modify tools, resources, and configurations. Wanaku also ensures secure access to the MCP tools and resources.
Wanaku uses Keycloak for authentication and authorization. As such, a Keycloak instance needs to be up and running for Wanaku to work. This section covers the basics of getting Keycloak ready for Wanaku for development and production purposes.
Choose the setup that matches your environment.
- Local Development: Use Podman for a quick, local instance.
- OpenShift Deployment: Follow these steps for a cluster environment.
This method is ideal for development and testing on your local machine.
First, run the following command in your terminal to start a Keycloak container. This command also sets the initial admin credentials and maps a local volume for data persistence.
podman run -d \
-p 127.0.0.1:8543:8080 \
-e KC_BOOTSTRAP_ADMIN_USERNAME=admin \
-e KC_BOOTSTRAP_ADMIN_PASSWORD=admin \
-v keycloak-dev:/opt/keycloak/data \
quay.io/keycloak/keycloak:26.3.5 start-dev-p 127.0.0.1:8543:8080: Maps port8543on your local machine to the container's port8080. By default, Wanaku expects Keycloak on port8543.-e ...: Sets the default admin username and password. Change the password for any non-trivial use case.-v keycloak-dev...: Creates a persistent volume namedkeycloak-devto store Keycloak data.
If you are deploying Wanaku in OpenShift or Kubernetes, you can follow these steps to get an entirely new Keycloak setup up and running. If you already have a Keycloak instance, you may skip the deployment section and jump to importing the realm.
Apply the pre-defined Kubernetes configurations located in the deploy/auth directory.
This will create all the necessary resources for Keycloak to run.
Important
Before applying, review the files and be sure to change the default admin password for security.
oc apply -f deploy/authThe simplest way to import the realm configuration is using the Wanaku CLI. You can set admin credentials once via environment variables:
export WANAKU_ADMIN_USERNAME=admin
export WANAKU_ADMIN_PASSWORD=admin
wanaku admin realm createThis imports the default realm configuration from deploy/auth/wanaku-config.json. You can specify a custom configuration file with --config /path/to/realm.json and a custom Keycloak URL with --keycloak-url.
Alternatively, Wanaku comes with a script that simplifies importing the realm configuration into keycloak.
To run that script:
- set the
WANAKU_KEYCLOAK_PASSvariable to the admin password of your Keycloak instance - set
WANAKU_KEYCLOAK_HOSTto the address of your Keycloak instance (i.e.;localhostif using Podman or the result ofoc get routes keycloak -o json | jq -r .spec.hostif using OpenShift)
Alternatively, you may also import the configuration using Keycloak's UI, and then proceed to regenerate the capabilities' client secret.
Finally, for security, you must regenerate the client secret for the wanaku-service client.
- Navigate to the Keycloak Admin Console at
http://localhost:8543. - Log in with your admin credentials (admin/admin).
- Select the wanaku realm from the dropdown in the top-left corner.
- Go to Clients in the side menu and click on wanaku-service.
- Go to the Credentials tab.
- Click the Regenerate secret button and confirm. Copy the new secret to use in your application's configuration.
To run Wanaku, you need to first download and install the router and the command line client.
Important: Java 21 or later is required to run Wanaku. Ensure you have Java 21+ installed before proceeding with the installation.
You can verify your Java version by running:
java -versionAlthough the router comes with a UI, the CLI is the primary method used to manage the router. As such, it's recommended to have it installed.
The most recommended method for installing the Wanaku CLI is to download the latest version directly from the release page on GitHub
To simplify using the Wanaku Command Line Interface (CLI), you can install it via JBang.
Note: JBang requires Java 21 or later for running Wanaku CLI.
First, ensure JBang is installed on your system. You can find detailed download and installation instructions on the official JBang website.
After installing JBang, verify it's working correctly by opening your command shell and running:
jbang versionThis command should display the installed version of JBang.
Next, to access the Wanaku CLI, install it using JBang with the following command:
jbang app install wanaku@wanaku-ai/wanakuThis will install Wanaku CLI as the wanaku command within JBang, meaning that you can run Wanaku from the command line by just
executing wanaku.
Note
It requires access to the internet, in case of using a proxy, please ensure that the proxy is configured for your system. If Wanaku JBang is not working with your current configuration, please look to Proxy configuration in JBang documentation.
There are three ways to run the router. They work similarly, with the distinction that some of them may come with more capabilities by default — continue reading the documentation below for details.
Important
Before the router can be executed, it still needs to be configured for secure access and control of its resources. Make sure you read the section [Securing the Wanaku MCP Router](# Securing the Wanaku MCP Router) before running or deploying the router.
You can use the Wanaku CLI to start a small/simplified local instance. To do so, you need to run and configure a local Keycloak
instance and then use the wanaku start local command to run Wanaku pointing to that instance. Make sure you follow the steps
described in [Option 1: Local Setup with Podman](## Option 1: Local Setup with Podman) the [Keycloak Setup For Wanaku](#Keycloak Setup for Wanaku).
After downloading the CLI, simply run wanaku start local and the CLI should download, deploy and start Wanaku with the main
server, a file provider and an HTTP provider. You will need to pass the client secret configured
so that the capabilities can connect to the router.
wanaku start local --capabilities-client-secret=aBqsU3EzUPCHumf9sTK5sanxXkB0yFtv
If that is successful, open your browser at http://localhost:8080, and you should have access to the UI.
Note
You can use the command line to enable more services by using the --services option. Use the --help to see the details.
The Wanaku Operator simplifies the deployment and management of Wanaku instances on Kubernetes and OpenShift clusters. It automates the creation and configuration of all necessary resources, making it the recommended approach for production deployments.
Before deploying the Wanaku Operator, ensure you have:
- Access to a Kubernetes or OpenShift cluster
kubectlorocCLI tools installed and configuredhelmCLI tool installed (version 3.x or later)- A running Keycloak instance (see Keycloak Setup for Wanaku)
- Sufficient permissions to create namespaces, deployments, and custom resources
The Wanaku Operator can be deployed using Helm charts. First, ensure you're in the correct namespace or create a new one:
kubectl create namespace wanakuThen, install the operator using the Helm chart from the repository:
helm install wanaku-operator ./wanaku-operator/deploy/helm/wanaku-operator \
--namespace wanaku \
--set operatorNamespace=wanakuBy default, the operator will be deployed in the namespace specified by the operatorNamespace value.
You can customize this during installation:
helm install wanaku-operator ./wanaku-operator/deploy/helm/wanaku-operator \
--namespace my-custom-namespace \
--set operatorNamespace=my-custom-namespaceTo verify the operator is running:
kubectl get pods -n wanakuYou should see the operator pod in a Running state.
Once the operator is installed, you can create Wanaku router instances by defining a custom resource. The operator watches for these custom resources and automatically creates all necessary Kubernetes objects.
Create a file named wanaku-instance.yaml with the following content:
apiVersion: "wanaku.ai/v1alpha1"
kind: Wanaku
metadata:
name: wanaku-dev
spec:
auth:
# This is the address of the authorization server (in the format: http://address)
authServer: http://keycloak:8080
# Address of the proxy (in the format: http://address).
# It could be the same as the auth server (default) or "auto"
# (for using Wanaku as the proxy via OIDC proxy)
# authProxy: ""
secrets:
# This is the OIDC credentials secret for the services
oidcCredentialsSecret: your-keycloak-client-secret
# Router settings are optional
router:
# You can set a custom image for the router
# image: quay.io/wanaku/wanaku-router-backend:latest
env:
# It is possible to set environment variables for the router
# - name: ENVIRONMENT_VARIABLE_1
# value: value1
# - name: ENVIRONMENT_VARIABLE_2
# value: value2
# Define the capabilities you want to enable
capabilities:
# HTTP capability for HTTP-based tools
- name: wanaku-http
image: quay.io/wanaku/wanaku-tool-service-http:latest
# Camel Integration Capability example
- name: employee-system
type: camel-integration-capability
image: quay.io/wanaku/camel-integration-capability:latest
env:
# The path to the routes file, should be within /data
- name: ROUTES_PATH
value: "/data/employee-routes.camel.yaml"
# The path to the rules file, should be within /data
- name: ROUTES_RULES
value: "/data/employee-rules.yaml"Apply the custom resource to create your Wanaku instance:
kubectl apply -f wanaku-instance.yamlThe operator will automatically create:
- Deployment for the Wanaku router
- Deployments for each enabled capability
- Services to expose the router and capabilities
- ConfigMaps for configuration
- Secrets for sensitive data
- Routes/Ingress (if configured)
- ServiceAccounts and RBAC resources
Note
When using the Camel Integration Capability, you can copy your route and rules files to the capability pods using:
kubectl cp your-routes.camel.yaml <pod-name>:/data/employee-routes.camel.yamlTip
You can find more complete examples in the wanaku-operator/samples directory.
To check the status of your Wanaku instance:
kubectl get wanaku -n wanakuTo view detailed information:
kubectl describe wanaku my-wanaku-router -n wanakuTo access the logs:
kubectl logs -n wanaku deployment/my-wanaku-routerOnce deployed, you can access the Wanaku router through its service. To get the service details:
kubectl get svc -n wanakuTo get the route URL:
oc get route my-wanaku-router -n wanaku -o jsonpath='{.spec.host}'To update your Wanaku instance, simply edit the custom resource and apply the changes:
kubectl edit wanaku my-wanaku-router -n wanakuOr update your YAML file and reapply:
kubectl apply -f wanaku-instance.yamlThe operator will automatically handle the update and roll out the changes.
To remove a Wanaku instance:
kubectl delete wanaku my-wanaku-router -n wanakuTo uninstall the operator:
helm uninstall wanaku-operator -n wanakuNote
The operator manages the entire lifecycle of Wanaku instances. Manual modifications to operator-managed resources may be overwritten by the operator's reconciliation process.
It is also possible to manually run Wanaku on Kubernetes distributions, such as OpenShift. The deployment is configured using Kustomize for environment-specific customization.
The basic steps to install and run Wanaku on OpenShift are:
- Download the kustomize template files in the
deploydirectory making sure to use the branch that matches your Wanaku version - Copy the files from the
devdirectory and use them to create a new overlay (i.e.:prod) - Adjust the kustomize files according to your environment.
Tip
You may also consult developer-specific documentation if you need special customizations to your deployment.
Wanaku is built on Quarkus and uses application.properties files for configuration. Each
component ships with built-in defaults, but you can override any property at runtime in three ways:
- External file: place an
application.propertiesin aconfig/directory next to the JAR - System properties: pass
-D<property>=<value>on the command line - Environment variables: export the property name in uppercase with dots/hyphens replaced by underscores
For example, to change the HTTP port:
# Via system property
java -Dquarkus.http.port=9090 -jar wanaku-router-backend-runner.jar
# Via environment variable
export QUARKUS_HTTP_PORT=9090
java -jar wanaku-router-backend-runner.jarFor the full list of available properties and more details on configuration precedence, see the Configuration Guide.
Wanaku also comes with a web user interface that you can access to manage the router. By default it runs on port 8080 of the host running the router.
Note
At this moment, some features are only available on the CLI.
When accessing the Web UI for the first time, you will be redirected to the Keycloak instance for login. Create a user and define a password.
Important
Wanaku does not yet support fine-grained control over its exposed resources. All users have admin access to the tools and resources exposed. Expect this to change in future versions.
Capabilities are standalone services that connect to the Wanaku router to provide new functionalities. They can be downloaded from the release page, deployed to OpenShift using containers or built from source.
To run a capability, you need to configure it to connect to your Wanaku router instance and authenticate with it. This is done by setting a few essential properties.
You can configure capabilities using environment variables, system properties on the command line, or by placing an
application.properties file in a config/ directory next to the capability JAR (see the
Configuration Basics section for details on how Quarkus loads configuration).
Here are the key properties you need to set:
-
Router URI: Each capability needs to know where the Wanaku router is located to register itself.
wanaku.service.registration.uri=http://localhost:8080 -
OIDC Client Credentials: Capabilities authenticate with the router using OIDC. You must provide the client secret that you previously regenerated in Keycloak.
quarkus.oidc-client.credentials.secret=your-client-secret-from-keycloak -
Announce Address (Optional): If the capability is running in an environment where its address is not directly accessible by the router (e.g., behind a NAT or in a container), you need to specify the address that the router should use to communicate back to it.
wanaku.service.registration.announce-address=your-public-address
Tip
You can check the full set of configuration available.
Once configured, you can run the capability from the command line. The following example shows how to run a capability while overriding the configuration properties:
java -Dwanaku.service.registration.uri=http://<wanaku-router-host>:8080 \
-Dquarkus.oidc-client.credentials.secret=<your-client-secret> \
-Dwanaku.service.registration.announce-address=<your-public-address> \
-jar <capability-jar-file>.jarNote
Each capability may have its own specific set of configurations. For example, the Camel Integration Capability for Wanaku requires additional properties to connect to different systems. Always consult the specific documentation for the capability you are using for more details.
Before deploying Wanaku on OpenShift, ensure you have:
- Access to an OpenShift or Kubernetes cluster
ocorkubectlCLI tools configured- Sufficient permissions to create deployments, services, and routes
You can deploy Wanaku in OpenShift or Kubernetes using Kustomize.
After having deployed Keycloak, then run the following command to get its route:
oc get route keycloak -o jsonpath='{.spec.host}'Lastly, copy the regenerated client secret and add it to the respective overlay:
oc apply -k deploy/openshift/kustomize/overlays/my-overlay/This updates the OIDC server URLs in the environment variable patch files to point to your Keycloak instance.
When running Wanaku on OpenShift or Kubernetes, capabilities cannot automatically discover the router address. You must configure the router location using environment variables in your deployment:
- Set
WANAKU_SERVICE_REGISTRATION_URIto point to the actual location of the router - Configure OIDC authentication URLs to point to your Keycloak instance
The Kustomize overlays handle these configurations automatically for different environments.
Important
This configuration is also required when running the router and the services on different hosts.
Security in Wanaku involves controlling access to the management APIs and web interface while ensuring that only authorized users can modify tools, resources, and configurations.
This section covers how to configure Wanaku for secure access.
Note
Authentication and authorization currently apply only to the management APIs and UI, not to the MCP endpoints themselves. This feature is experimental and under active development.
Wanaku's security model focuses on:
- API Protection: Securing management operations for tools, resources, and configuration
- UI Access Control: Restricting access to the web console
- Service Authentication: Ensuring capability services can authenticate with the router
- MCP Authentication: Ensuring MCP calls are authenticated
Currently, Wanaku supports:
- OAuth authentication with code grant
- Automatic client registration
Important
When using the Automatic client registration, the access is granted per-namespace. As such, applications need to request a new client id and grant if they change the namespace in use.
For these to work, Keycloak needs to be configured so that the authentication is properly supported.
Wanaku comes with a template configuration that can be imported into Keycloak to set up the realm, clients and everything else needed for Wanaku to work.
Important
After importing this, make sure to adjust the secrets used by the services and any other potential sensitive configuration.
When connecting an MCP client application to Wanaku, you need to configure it with the correct OIDC client ID and scopes. By default, the Wanaku Keycloak realm provides the following settings for MCP clients:
- Client ID:
mcp-client - Scopes:
openid,wanaku-mcp-client
When an application uses these settings to connect to a Wanaku MCP endpoint, the user will be redirected to the Keycloak login page. After entering their username and password, Keycloak will redirect them back to the application with a valid authentication token.
Note
If using automatic client registration, the registered client will use these same defaults. Applications only need to request a new client ID and grant when changing the namespace in use.
Each Wanaku component requires a specific set of configurations for secure access. You can find the full set of configuration options in the Configuration Guide.
The configuration varies depending on the component's role in the system.
The backend service handles API operations and requires OIDC configuration with service credentials. Some of the configurations you may need to change are:
# Address of the Keycloak authentication server - adjust to your Keycloak instance
auth.server=http://localhost:8543
# Address used by the OIDC proxy -
auth.proxy=http://localhost:${quarkus.http.port}
# Client identifier configured in Keycloak for the backend service
quarkus.oidc.client-id=wanaku-mcp-router
# Avoid forcing HTTPS
quarkus.oidc.resource-metadata.force-https-scheme=falseAs a reference for understanding what is going on under the hood, the following guides may be helpful:
Wanaku also requires for the capabilities services to be authenticated in order to register themselves. Capability services act as OIDC clients and authenticate with the router using client credentials. Some of the settings you may need to adjust are:
# Address of the Keycloak authentication server - adjust to your Keycloak instance
auth.server=http://localhost:8543
# Address of the KeyCloak authentication server
quarkus.oidc-client.auth-server-url=${auth.server}/realms/wanaku
# Client secret from Keycloak for service authentication - replace with your actual secret
quarkus.oidc-client.credentials.secret=aBqsU3EzUPCHumf9sTK5sanxXkB0yFtvImportant
- Capability services use the OIDC client component (
quarkus.oidc-client.*), which differs from the main router configuration - The client secret values shown here are examples from the default configuration - replace them with your actual Keycloak client secrets
- Ensure the auth-server-url points to your actual Keycloak instance
Wanaku supports AES-256 encryption for secrets stored in files. When enabled, all secrets provisioned by tools and resources are encrypted before being written to disk and automatically decrypted when read.
To enable secret encryption, set both environment variables:
export WANAKU_SECRETS_ENCRYPTION_PASSWORD="your-strong-password"
export WANAKU_SECRETS_ENCRYPTION_SALT="unique-salt-value"Important
- Both password and salt must be set for encryption to work
- All services that handle secrets must use the same password and salt values
- Store credentials securely (e.g., Kubernetes Secrets, HashiCorp Vault)
Warning
If the encryption password or salt is lost, encrypted secrets cannot be recovered. Ensure these values are backed up securely.
For more details, see the Configuration Guide.
Wanaku supports MCP via SSE (deprecated) or via Streamable HTTP.
the MCP endpoint exposed by Wanaku can be accessed on the path /mcp/sse of the host you are using (for instance, if running
locally, that would mean http://localhost:8080/mcp/sse).
The Streamable HTTP endpoint can be accessed on the path /mcp/.
Important
Also make sure to check the details about namespaces, as Wanaku offers different namespaces where MCP Tools and MCP Resources can be registered. This is documented further ahead in this guide.
The Wanaku CLI supports authentication to securely interact with the Wanaku MCP Router API. Authentication credentials are stored locally and automatically included in API requests.
The CLI currently supports the following authentication modes:
- token (default): Use an API token for authentication via Bearer token
- username and password
Store authentication credentials for use with subsequent CLI commands:
wanaku auth login --api-token <your-api-token>Options:
--api-token <token>: API token for authentication (required)--auth-server <url>: Authentication server URL (optional)--mode <mode>: Authentication mode -tokenoroauth2(default:token)
Example:
wanaku auth login --api-token eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9...With custom authentication server:
wanaku auth login \
--api-token eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9... \
--auth-server https://keycloak.example.com \
--mode tokenCheck the current authentication status and view stored credentials:
wanaku auth statusThis command displays:
- Current authentication mode
- Masked API token (showing first and last 4 characters)
- Authentication server URL (if configured)
- Masked refresh token (if available)
- Credentials file location
- Whether credentials are currently stored
Example output:
Authentication Status:
=====================
Mode: token
API Token: eyJh***VCJ9
Auth Server: https://keycloak.example.com
Credentials File: /Users/username/.wanaku/credentials
Has Credentials: true
Clear all stored authentication credentials:
wanaku auth logoutThis command removes all authentication data from the local credentials file.
Display the raw authentication token (useful for debugging or using with other tools):
wanaku auth tokenThis outputs the raw API token without masking.
Once authenticated via wanaku auth login, all subsequent CLI commands will automatically include the authentication token in their requests.
You can override the stored authentication token for a single command:
wanaku tools list --token <temporary-token>To explicitly disable authentication for a command:
wanaku tools list --no-authAuthentication credentials are stored in:
~/.wanaku/credentials
This file is a Java properties file containing:
api.token: The API bearer tokenrefresh.token: OAuth2 refresh token (when applicable)auth.mode: The authentication mode (token, oauth2, etc.)auth.server.url: The authentication server URL
Caution
The credentials file contains sensitive authentication tokens. Ensure proper file permissions are set to prevent unauthorized access.
On Unix-like systems, you should restrict access: chmod 600 ~/.wanaku/credentials
The CLI authentication process works as follows:
- Login: User provides API token via
wanaku auth login --api-token <token> - Storage: Token is stored in
~/.wanaku/credentials - Auto-Injection: The CLI automatically reads the token and adds it as a Bearer token to the
Authorizationheader for all API requests - Validation: The Wanaku Router validates the token on each request
- Logout: User can clear credentials via
wanaku auth logout
If you receive authentication errors:
-
Check token validity:
wanaku auth status
-
Verify the token hasn't expired
-
Ensure you're using the correct authentication server URL
-
Try logging in again with a fresh token
To completely reset authentication:
wanaku auth logout
wanaku auth login --api-token <new-token>You can manually edit or remove the credentials file if needed:
# View credentials
cat ~/.wanaku/credentials
# Remove credentials manually
rm ~/.wanaku/credentials- Token Protection: Never share your API tokens or commit them to version control
- Regular Rotation: Rotate tokens periodically for enhanced security
- Use Environment Variables: For CI/CD, consider using
--tokenflag with environment variables instead of storing tokens - File Permissions: Ensure credentials file has restricted permissions (600)
- Logout When Done: Use
wanaku auth logoutwhen finished working on shared systems
# Login with API token
wanaku auth login --api-token eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9...
# Verify authentication
wanaku auth status
# Use authenticated commands
wanaku tools list
wanaku resources list
wanaku data-store list
# Logout when done
wanaku auth logoutFor automated scripts, use token override instead of storing credentials:
# Use token from environment variable
wanaku tools list --token $WANAKU_API_TOKEN
# Or disable authentication for public endpoints
wanaku tools list --no-authThe wanaku admin command group provides Keycloak administration operations for managing realms, users, and service client credentials. These commands authenticate directly against Keycloak using admin credentials rather than the user's stored token.
All admin commands share the following options:
| Option | Description | Default |
|---|---|---|
--admin-username |
Admin username for Keycloak (required unless WANAKU_ADMIN_USERNAME is set) |
|
--admin-password |
Admin password for Keycloak (required unless WANAKU_ADMIN_PASSWORD is set, interactive) |
|
--keycloak-url |
Keycloak server URL | http://localhost:8543 |
--realm |
Keycloak realm to manage | wanaku |
If you prefer not to pass admin credentials on every command, set them once in your environment:
export WANAKU_ADMIN_USERNAME=admin
export WANAKU_ADMIN_PASSWORD=admin
wanaku admin users list# List all users in the realm
wanaku admin users list --admin-username admin --admin-password admin
# Create a new user
wanaku admin users add --admin-username admin --admin-password admin \
--username alice --password secretpass --email alice@example.com
# Remove a user
wanaku admin users remove --admin-username admin --admin-password admin \
--username alice
# Set a user's password
wanaku admin users set-password --admin-username admin --admin-password admin \
--username alice --password newpass# List service clients (filters out internal Keycloak clients)
wanaku admin credentials list --admin-username admin --admin-password admin
# Create a new service client
wanaku admin credentials add --admin-username admin --admin-password admin \
--client-id my-service --description "My service client"
# Create a service client and display its secret
wanaku admin credentials add --admin-username admin --admin-password admin \
--client-id my-service --show-secret
# Show an existing client's secret
wanaku admin credentials show --admin-username admin --admin-password admin \
--client-id my-service --show-secret
# Regenerate a client's secret
wanaku admin credentials regenerate --admin-username admin --admin-password admin \
--client-id my-service --show-secret
# Remove a service client
wanaku admin credentials remove --admin-username admin --admin-password admin \
--client-id my-serviceNote: The
--show-secretflag is required to display client secrets. Without it,credentials showwill print a warning instead. Use with caution as secrets may leak into logs or shell history.
# Import the default realm configuration (deploy/auth/wanaku-config.json)
wanaku admin realm create --admin-username admin --admin-password admin
# Import a custom realm configuration file
wanaku admin realm create --admin-username admin --admin-password admin \
--config /path/to/realm.json
# Import with a custom Keycloak URL
wanaku admin realm create --keycloak-url http://keycloak:8080 \
--admin-username admin --admin-password adminWanaku itself does not have any builtin MCP tool, resource or functionality itself. The router itself is just a blank MCP server.
To actually perform its work, Wanaku relies on specialized services that offer the connectivity bridge that enables Wanaku to talk to any kind of service. At its core, Wanaku is powered by Quarkus and Apache Camel, which provide the ability to connect to more than 300 different types of systems and services.
The power of Wanaku relies on its ability to plug in different types of systems, regardless of them being new microservices or legacy enterprise systems. For instance, consider the scenario of an enterprise organization, which is running hundreds of systems. With Wanaku, it is possible to create a specific capability for each of them (i.e.: a capability for the finance systems, another for human resources, another for billing, and so on).
The granularity on which these capabilities can operate is a decision left to the administrator of the system. For some organizations, having a "Kafka" capability to Wanaku capable of talking to any of its systems may be enough. Others, may want to have system-specific ones (i.e.: a billing capability, an employee system capability, etc).
The recommended way to create those capabilities is to use the Camel Integration Capability for Wanaku. This is a subcomponent of Wanaku that leverages Apache Camel to exchange data with any system that Camel is capable of talking to.
Note
Capabilities were, at some point, also called "Downstream services" or "targets". You may still see that terminology used in some places, especially in older documentation.
You should see a list of capabilities available in the UI, in the Capabilities page. Something similar to this:
On the CLI, running wanaku capabilities list lists the capabilities available for MCP tools:
service serviceType host port status lastSeen
exec tool-invoker 127.0.0.1 9009 active Sat, Oct 18, 2025 at 18:47:22
http tool-invoker 127.0.0.1 9000 active Sat, Oct 18, 2025 at 18:47:23
tavily tool-invoker 127.0.0.1 9006 active Sat, Oct 18, 2025 at 18:47:23Capabilities determine what type of tools you may add to the router. As such, in the output from the CLI above, it means that
this server can add tools of the following types: exec, tavily, and http.
Wanaku accepts the following capability service types:
tool-invoker: these capabilities can be used to create MCP tools.resource-provider: these capabilities can be used to create MCP resources.multi-capability: these capabilities can be used to create either MCP tools or MCP resources.
An MCP (Model Context Protocol) tool enables Large Language Models (LLMs) to execute tasks beyond their inherent capabilities by using external functions. Each tool is uniquely identified by a name and defined with an input schema that outlines the expected parameters. Essentially, MCP tools act as a standardized interface through which an AI agent can request information or execute specific tasks from external systems, like APIs or databases.
When adding a tool to Wanaku, there are two key considerations:
- Capability: determine which capability will handle the request and process the input data.
- Tool/Service Arguments: Identify any arguments (also known as properties) that the tool and/or service accept.
A capability service is required to be available at the moment when a new tool is being added to Wanaku MCP Router.
To add a new tool to a Wanaku MCP Router Backend instance running locally on http://localhost:8080, use the following command:
wanaku tools add -n "meow-facts" --description "Retrieve random facts about cats" --uri "https://meowfacts.herokuapp.com?count={parameter.valueOrElse('count', 1)}" --type http --property "count:int,The count of facts to retrieve" --required countThe command wanaku tools add is used to register a new tool with the Wanaku MCP Router. Let's break down each part of the command:
-n "meow-facts": This flag sets the name of the tool to "meow-facts". This is a unique, human-readable identifier for the tool.--description "Retrieve random facts about cats": This provides a description of what the tool does, making it clear for users and LLMs.--uri "https://meowfacts.herokuapp.com?count={parameter.valueOrElse('count', 1)}": This specifies the URI (Uniform Resource Identifier) that the tool will interact with. In this case, it's an HTTP endpoint that provides cat facts. The {parameter.valueOrElse('count', 1)} part indicates that the count parameter from the tool's input will be used in the URI. If count is not provided, it will default to 1. This demonstrates how Wanaku can dynamically build URIs with parameters.--type http: This defines the type of the tool's underlying service, which in this case ishttp. This tells Wanaku that it should use its HTTP service handling capabilities for this tool.--property "count:int,The count of facts to retrieve": This defines an input property for the tool named count. It specifies that count is an integer (int) and provides a description of what it represents:"The count of facts to retrieve".--required count: This flag indicates that the count property is a required input for this tool.
You can organize and categorize your tools using labels. Labels are key-value pairs that help you filter and manage tools more effectively:
wanaku tools add -n "weather-api" --description "Get weather forecast" --uri "https://api.weather.com/forecast" --type http --label category=weather --label environment=production --label region=us-eastLabels can be used for:
- Categorization: Group tools by function (e.g.,
category=weather,category=finance) - Environment tracking: Identify deployment environments (e.g.,
environment=production,environment=staging) - Access control: Tag tools by team or department (e.g.,
team=engineering,team=sales) - Lifecycle management: Mark tools for deprecation or testing (e.g.,
status=deprecated,status=beta)
You can add multiple labels by repeating the --label flag, using the format --label key=value.
After creating tools, you can add or remove labels without modifying the tool definition:
Adding labels to an existing tool:
# Add labels to a specific tool
wanaku tools label add --name "weather-api" --label priority=high --label reviewed=true
# Add labels to multiple tools using label expressions (-e is short for --label-expression)
wanaku tools label add -e 'category=weather' --label migrated=trueRemoving labels from an existing tool:
# Remove labels from a specific tool
wanaku tools label remove --name "weather-api" --label temporary --label draft
# Remove labels from multiple tools using label expressions (-e is short for --label-expression)
wanaku tools label remove -e 'status=deprecated' --label legacyNote: When adding a label with a key that already exists, the value will be updated. When removing a non-existent label, it will be silently ignored.
Note
For remote instances, you can use the parameter --host to point to the location of the instance.
Important
The meaning of the uri and how to actually compose it, depends on the type of capability being used. Each capability describes
exactly the meaning of the URI, so make sure to check the capability service for details. Additionally, this is covered in more
details in the Creating URIs section below.
Sometimes, specific configurations are required for the downstream services (capabilities) that a tool uses. This might include setting timeouts for operations or providing credentials to access a particular resource.
In such scenarios, you can associate configuration and secret files directly with a tool. These files will be automatically used by the underlying capabilities each time the tool is invoked.
Here's an example of how to add a tool and link it to configuration and secret files:
wanaku tools add --host http://localhost:8080 -n "meow-facts" --description "Retrieve random facts about cats" --uri "https://meowfacts.herokuapp.com?count={count or 1}" --type http --property "count:int,The count of facts to retrieve" --required count --configuration-from-file capabilities.properties --secrets-from-file secret.propertiesIn this command:
--configuration-from-file capabilities.properties: This flag specifies a file namedcapabilities.propertiesthat contains configuration settings to be passed to the underlying capability whenever the"meow-facts"tool is used.--secrets-from-file secret.properties: This flag points to a file namedsecret.propertiesthat holds sensitive information (like API keys or passwords) needed by the capability to access resources, ensuring secure handling of credentials.
Some capabilities within Wanaku are designed to interpret these configuration settings to dynamically adjust how they interact
with external systems.
For instance, Camel-based capabilities leverage these settings, particularly those prefixed with query., to modify the Camel
URI used for the endpoint.
Consider the following example in a configuration file:
key=value
query.addKey=addedValueIn this scenario, a Camel-based capability would automatically append addKey=addValue to the URI passed to the underlying
Camel producer.
This allows for flexible and dynamic adjustment of endpoint parameters based on the provided configuration.
Secrets behave just as similarly, but are adapted by the capabilities for secure handling of the data.
It is also possible to add new tools using the UI, by accessing the Tools page and filling the form.
Wanaku ToolSets are collections of tools that can be easily shared and imported into your Wanaku router. This feature allows for convenient distribution of pre-configured tools among users.
Wanaku provides a selection of ready-to-use ToolSets that you can import to quickly get started and explore its functionalities.
To import a ToolSet directly into your router from a URL, use the following command:
wanaku tools import https://raw.githubusercontent.com/wanaku-ai/wanaku-toolsets/refs/heads/main/toolsets/currency.jsonIf you have a ToolSet definition file already stored on your local machine, you can import it using its file path:
wanaku tools import /path/to/the/toolsets/currency.jsonYou can check what tools are available in a Wanaku MCP Router instance by running:
wanaku tools listThe wanaku tools edit command enables you to modify the existing definition of a tool that is registered with your Wanaku MCP
Router.
This command provides a convenient way to update a tool's JSON definition directly within your terminal using the nano text editor.
wanaku tools edit [options] [toolName]In this command:
toolName: (Optional) Specifies the exact name of the tool you wish to modify. If this argument is omitted, the command will present you with an interactive, scrollable list of all currently registered tools, allowing for easy selection.
If you know the precise name of the tool you want to edit, you can specify it directly.
For example, to edit a tool named "my-custom-tool":
wanaku tools edit my-custom-toolUpon executing this command, Wanaku will fetch the JSON definition of "my-custom-tool" and open it in the nano editor within
your terminal.
After making your desired changes, save them (usually by pressing Ctrl+S) and then exit nano (Ctrl+X).
Wanaku will then ask for your confirmation before applying the updates to the tool's definition.
When you're unsure of the exact tool name or want to browse available tools, run the edit command without specifying a toolName:
wanaku tools editThis will present an interactive, scrollable list of all your registered tools.
Use your keyboard's arrow keys to navigate and highlight the tool you wish to edit, then press Enter.
The selected tool's JSON definition will then open in nano for you to make your modifications.
Any available tool is listed by default when you access the UI.
When using the CLI, the wanaku tools list command allows you to view all available tools on your Wanaku MCP Router instance.
Running this command will display a comprehensive list of tools, including their names and descriptions.
wanaku tools listFor example, you should receive an output similar to this.
Name Type URI
meow-facts => http => https://meowfacts.herokuapp.com?count={parameter.valueOrElse('count', 1)}
dog-facts => http => https://dogapi.dog/api/v2/facts?limit={parameter.valueOrElse('count', 1)}The wanaku tools show command displays detailed information about a specific tool registered in the Wanaku MCP Router.
wanaku tools show <tool-name>This command retrieves comprehensive details including the tool's name, namespace, type, description, URI, labels, and input schema properties.
Example:
wanaku tools show meow-factsSample Output:
Tool Details:
name meow-facts
namespace default
type http
description Retrieve random facts about cats
uri https://meowfacts.herokuapp.com?count={parameter.valueOrElse('count', 1)}
labels category=animals
Input Schema Properties:
name type description required
count int The count of facts to retrieve yes
Options:
--host <url>: The API host URL (default:http://localhost:8080)
Example with remote host:
wanaku tools show --host http://api.example.com:8080 meow-factsTools can be removed from the UI by clicking on the Trash icon, or via the CLI using the wanaku tools remove command.
To remove a specific tool by name:
wanaku tools remove --name "meow-facts"You can remove multiple tools at once using label expressions. This is particularly useful for cleaning up tools by category, environment, or other criteria:
wanaku tools remove -e 'category=weather'This command will:
- Find all tools with the label
category=weather - Display a preview table showing which tools will be removed
- Prompt for confirmation before removal
- Report the number of tools removed
Advanced Label Expression Examples:
Remove all non-production tools:
wanaku tools remove -e 'environment!=production'Remove deprecated weather tools:
wanaku tools remove -e 'category=weather & status=deprecated'Remove tools from either development or staging environments:
wanaku tools remove -e 'environment=development | environment=staging'Remove deprecated tools in multiple categories:
wanaku tools remove -e '(category=weather | category=news) & status=deprecated'Label Expression Syntax:
key=value- Equalskey!=value- Not equalsexpr1 & expr2- Logical ANDexpr1 | expr2- Logical OR!expr- Logical NOT(expr)- Grouping
Skipping Confirmation:
For automated scripts, you can skip the confirmation prompt using the --assume-yes or -y flag:
wanaku tools remove -e 'status=deprecated' -yWarning
Batch removal operations cannot be undone. Always review the preview table carefully before confirming removal.
For detailed information about label expression syntax, see:
wanaku man label-expressionThe wanaku tools generate command converts an OpenAPI specification into a collection of tool references
that can be used by an AI agent.
It parses and resolves OpenAPI paths and operations, transforming them into a standardized tool reference format for HTTP services.
This command accepts an OpenAPI specification file (either as a local path or URL) and produces a JSON output containing tool references.
Each operation in the API is converted to a tool reference with appropriate metadata, including the operation's name, description, URI template, and input schema.
The command handles server variable substitution, proper formatting of path parameters according to the tool reference specification.
By default, the command uses the first server defined in the OpenAPI specification, but you can override this behavior by specifying a different server URL or selecting a different server from the specification by index.
The generated output can be directed to standard output or saved to a file.
If the process completes successfully, the command returns exit code 0. It returns exit code 3 if no paths are found in the
specification and exit code 2 if an error occurs during processing.
Note
The command support both json and yaml definition:
For example:
wanaku tools generate http://petstore3.swagger.io/api/v3/openapi.yamlIf the spec defines a server url that contains variables
servers:
- url: 'https://{env}.domain.com/foo/{v1}/{v2}/{v3}'
variables:
env:
description: Environment - staging or production
default: stage-api
enum:
- stage-api
- api
# other variables
# ...Then, you can specify values as command parameters:
wanaku tools generate --server-variable env=prod --server-variable v1=first http://petstore3.swagger.io/api/v3/openapi.jsonIf not specified for a variable in the server URL template, the default value defined in the OpenAPI specification will be used.
It only applies when using servers from the OpenAPI specification (not when using --server-url).
Variables must be defined in the server object of the OpenAPI specification.
Empty or null values for either key or value will be ignored.
OpenAPI specifications can define multiple server URLs:
{
"servers": [
{
"url": "https://api.example.com/v1",
"description": "Production server"
},
{
"url": "https://staging-api.example.com/v1",
"description": "Staging server"
},
{
"url": "http://localhost:8080/v1",
"description": "Local development server"
}
]
}The --server-index (or -i) option allows you to specify which server definition from the OpenAPI specification should be
used as the base URL for tool references.
wanaku tools generate -i 1 ./openapi-spec.yamlThis option is ignored if --server-url is specified, as an explicit URL overrides any server definitions in the
specification.
If neither --server-index nor --server-url is specified, the command will default to using the first server (index 0)
from the specification.
The --server-index option can be used together with --server-variable when the selected server has variable templates:
servers:
- url: https://{environment}.api.example.com/{version}
variables:
environment:
default: dev
version:
default: v1
- url: https://{environment}.api2.example.com/{version}
variables:
environment:
default: dev
version:
default: v1
- url: https://{environment}.api3.example.com/{version}
variables:
environment:
default: dev
version:
default: v1 You could select this server and override its variables:
wanaku tools generate -i 0 -v environment=prod -v version=v2 ./openapi-spec.yamlThe --output-file (or -o) option specifies the file path where the generated tool references should be written.
It determines where the output JSON containing all the tool references will be saved.
wanaku tools generate -o ./toolsets/api-tools.json http://petstore3.swagger.io/api/v3/openapi.jsonIf --output-file is specified, the command will write the JSON toolset to the specified file path.
If --output-file is not specified, the command will write the JSON toolset to standard output (STDOUT).
If the specified path is a directory, the command will write to a file named out.json within that directory and provide
a warning message.
If the specified file already exists, the command will return an error without overwriting the file. The parent directory of the specified file must exist and be writable by the current user.
If the --import (or -I) option is set, the generated toolset is automatically imported into the router, equivalent
to running the generate command followed by the import command.
The wanaku resources expose command allows you to make an existing resource available via your Wanaku MCP Router instance.
Just like tools, it also requires a capability that can access the system storing and providing access to the resource (i.e.: FTP, AWS S3, NFS, etc.).
For example, suppose you have a file named test-mcp-2.txt on your home directory on host that has the file capability running,
and you want to expose it.
This is how you can do it:
wanaku resources expose --location=$HOME/test-mcp-2.txt --mimeType=text/plain --description="Sample resource added via CLI" --name="test mcp via CLI" --type=fileIn this example:
--location=$HOME/test-mcp-2.txt: Specifies the local path to the resource you want to expose.--mimeType=text/plain: Defines the MIME type of the resource, indicating its content format.--description="Sample resource added via CLI": Provides a descriptive text for the resource.--name="test mcp via CLI": Assigns a human-readable name to the exposed resource.--type=file: Indicates that the exposed resource is a file.
Just like tools, you can organize resources using labels:
wanaku resources expose --location=$HOME/documents/report.pdf --mimeType=application/pdf --description="Q4 Financial Report" --name="q4-report" --type=file --label category=finance --label year=2024 --label department=accountingLabels help you:
- Organize resources by category, department, or project
- Track resource lifecycles and versions
- Filter and manage resources more effectively
- Implement batch operations on groups of resources
Important
It's important to note that this location refers to a location that the capability (downstream service) is able to access. The exact meaning of "location" depends on the type of the capability. For example:
- For a
filetype, it means the capability needs direct access to the file, implying it's likely running on a host with direct physical access to the file. - For an
ftptype, it means the capability needs access to the FTP server storing the file.
Always check the documentation for the capability provider that you are using for additional details about the location specifier.
After creating resources, you can add or remove labels without modifying the resource definition:
Adding labels to an existing resource:
# Add labels to a specific resource
wanaku resources label add --name "q4-report" --label archived=true --label reviewed=yes
# Add labels to multiple resources using label expressions (-e is short for --label-expression)
wanaku resources label add -e 'category=finance' --label migrated=trueRemoving labels from an existing resource:
# Remove labels from a specific resource
wanaku resources label remove --name "q4-report" --label temporary --label draft
# Remove labels from multiple resources using label expressions (-e is short for --label-expression)
wanaku resources label remove -e 'status=archived' --label legacyNote: When adding a label with a key that already exists, the value will be updated. When removing a non-existent label, it will be silently ignored.
The wanaku resources list command allows you to view all resources currently exposed by your Wanaku MCP Router instance.
Executing this command will display a list of available resources, including their names and descriptions.
wanaku resources listThe wanaku resources show command displays detailed information about a specific resource registered in the Wanaku MCP Router.
wanaku resources show <resource-name>This command retrieves comprehensive details including the resource's name, type, description, location, MIME type, namespace, labels, and parameters.
Example:
wanaku resources show q4-reportSample Output:
Resource Details:
name q4-report
type file
description Q4 Financial Report
location /home/user/documents/report.pdf
mimeType application/pdf
namespace default
labels category=finance, year=2024
Parameters:
name value
key1 value1
key2 value2
Options:
--host <url>: The API host URL (default:http://localhost:8080)
Example with remote host:
wanaku resources show --host http://api.example.com:8080 q4-reportPrompts are reusable templates that can leverage multiple tools and provide example interactions for LLMs. They are part of the MCP (Model Context Protocol) specification and enable:
- Creating standardized message templates with variable substitution
- Defining argument schemas for dynamic prompt generation
- Referencing tools that the prompt can utilize
- Supporting multiple content types (text, images, audio, embedded resources)
- Providing example interactions to guide LLM behavior
The wanaku prompts add command allows you to create new prompts in your Wanaku MCP Router instance.
wanaku prompts add \
--name "code-review" \
--description "Review code for quality and security issues" \
--message "user:text:Please review the following code: {{code}}" \
--message "assistant:text:I'll analyze this code for potential issues." \
--argument "code:The code to review:true"In this example:
--name "code-review": Assigns a unique identifier for the prompt--description: Provides a human-readable description--message: Defines messages in the prompt (can be specified multiple times)--argument: Defines template arguments (format:name:description:required)
The --message option supports multiple content types:
Text Messages (default):
--message "user:text:Your message here"
--message "user:Your message here" # Backward compatible shorthandImage Messages:
--message "user:image:iVBORw0KGgoAAAANSUhEUgAAAAUA...:image/png"Audio Messages:
--message "user:audio:UklGRiQAAABXQVZFZm10IBAAAA...:audio/wav"Embedded Resource Messages:
--message "user:resource:file:///path/to/file.txt:File content:text/plain"Prompts support Mustache-style variable substitution using {{variable}} syntax:
wanaku prompts add \
--name "translate" \
--description "Translate text between languages" \
--message "user:text:Translate the following text from {{source_lang}} to {{target_lang}}: {{text}}" \
--argument "source_lang:Source language:true" \
--argument "target_lang:Target language:true" \
--argument "text:Text to translate:true"Prompts can reference specific tools they may utilize:
wanaku prompts add \
--name "api-test" \
--description "Test API endpoints" \
--message "user:text:Test the API endpoint {{endpoint}}" \
--tool-reference "http-get" \
--tool-reference "http-post" \
--argument "endpoint:API endpoint URL:true"Prompts can be organized into namespaces for isolation:
wanaku prompts add \
--name "review" \
--description "Code review prompt" \
--namespace "ns-0" \
--message "user:text:Review this code: {{code}}" \
--argument "code:Code to review:true"Supported namespaces: ns-0 through ns-9, default, and public.
You can also manage prompts through the Wanaku Web UI:
- Navigate to the Prompts page in the Web UI
- Click "Add Prompt"
- Fill in the form:
- Name: Unique identifier for the prompt
- Description: Human-readable description
- Messages (JSON): Array of message objects
- Arguments (JSON): Array of argument objects (optional)
- Tool References (JSON): Array of tool names (optional)
- Namespace: Namespace for isolation (optional)
Example message JSON formats:
Text Message:
{
"role": "user",
"content": {
"type": "text",
"text": "Review {{code}}"
}
}Image Message:
{
"role": "user",
"content": {
"type": "image",
"data": "iVBORw0KGgoAAAANSUhEUgAAAAUA...",
"mimeType": "image/png"
}
}Audio Message:
{
"role": "user",
"content": {
"type": "audio",
"data": "UklGRiQAAABXQVZFZm10IBAAAA...",
"mimeType": "audio/wav"
}
}Embedded Resource Message:
{
"role": "user",
"content": {
"type": "resource",
"resource": {
"location": "file:///path/to/file.txt",
"description": "File content",
"mimeType": "text/plain"
}
}
}View all prompts currently available in your Wanaku MCP Router instance:
wanaku prompts listThis displays all prompts with their names, descriptions, and namespaces.
You can edit an existing prompt using the CLI.
The wanaku prompts edit command allows you to modify an existing prompt. Only the fields you specify will be updated:
wanaku prompts edit \
--name "code-review" \
--description "Updated description for code review" \
--message "user:text:Please review this code: {{code}}"All options except --name are optional:
- If
--descriptionis provided, it replaces the existing description - If
--messageis provided, it replaces all existing messages - If
--argumentis provided, it replaces all existing arguments - If
--tool-referencesis provided, it replaces all existing tool references - If
--namespaceis provided, it replaces the existing namespace
Example of updating only the description:
wanaku prompts edit --name "code-review" --description "New description"Example of updating messages:
wanaku prompts edit \
--name "code-review" \
--message "user:text:Review the following code for security issues: {{code}}" \
--message "assistant:text:I'll perform a security audit."Remove a prompt by name:
wanaku prompts remove --name "code-review"Resources can be removed from the UI or via the CLI using the wanaku resources remove command.
To remove a specific resource by name:
wanaku resources remove --name "q4-report"Similar to tools, you can remove multiple resources at once using label expressions:
wanaku resources remove -e 'year=2023'This command will:
- Find all resources with the label
year=2023 - Display a preview table showing which resources will be removed
- Prompt for confirmation before removal
- Report the number of resources removed
Examples:
Remove all draft documents:
wanaku resources remove -e 'status=draft'Remove archived resources from a specific department:
wanaku resources remove -e 'department=sales & status=archived'Remove resources that are not marked as important:
wanaku resources remove -e '!priority=high'For automated scripts, skip the confirmation prompt:
wanaku resources remove -e 'year=2022' -yWarning
Resource removal operations cannot be undone. Always review the preview table before confirming removal.
Wanaku provides a data store feature that allows you to share static data between Wanaku and its capabilities.
This is particularly useful for storing configuration files, route definitions, and other static resources that capabilities need to access at runtime.
A primary use case for the data store is storing Apache Camel routes and associated files for the Camel Integration Capability.
By storing route definitions in the data store, you can dynamically configure integrations without rebuilding or redeploying capabilities.
Important
Authentication is required to access the data store API.
Make sure you're logged in using wanaku auth login before using data store commands.
The wanaku data-store add command allows you to upload files to the data store.
Files are automatically Base64 encoded when stored.
wanaku data-store add --read-from-file /path/to/file.yamlBy default, the data store entry will be named after the filename. You can specify a custom name using the --name option:
wanaku data-store add --read-from-file /path/to/employee-routes.camel.yaml --name employee-routesIn this example:
--read-from-file: Specifies the local file path to upload--name: (Optional) Assigns a custom name to the stored data
The file contents are automatically Base64 encoded before being sent to the server, ensuring binary-safe storage.
View all data currently stored in the data store:
wanaku data-store listThis displays a table showing:
- ID: Unique identifier for each stored item
- Name: The name of the stored data
- Data: A preview of the stored content (truncated to 50 characters)
- Labels: Labels associated with the data store entry
You can filter the list using label expressions:
# Filter by label expression
wanaku data-store list -e 'category=routes'See the label expression guide (wanaku man label-expression) for detailed syntax information.
Data stores support labels for organization and filtering, similar to tools and resources.
Adding labels to a data store:
# Add labels to a specific data store by ID
wanaku data-store label add --id <data-store-id> --label category=routes --label env=production
# Add labels to multiple data stores using label expressions
wanaku data-store label add -e 'category=config' --label migrated=trueRemoving labels from a data store:
# Remove labels from a specific data store by ID
wanaku data-store label remove --id <data-store-id> --label temporary --label draft
# Remove labels from multiple data stores using label expressions
wanaku data-store label remove -e 'status=deprecated' --label legacyWhen adding a label with a key that already exists, the value will be updated. When removing a non-existent label, it will be silently ignored.
Remove stored data using either the ID or name:
# Remove by ID
wanaku data-store remove --id <data-store-id>
# Remove by name
wanaku data-store remove --name employee-routesNote
The data store is also accessible via the REST API at /api/v1/data-store and through the Wanaku web interface under the Data Stores page,
where you can upload, download, and manage stored data using a graphical interface.
Configurations in Wanaku have two distinct scopes:
- Capability service configurations
- Tool definition configurations
These configurations are essential for setting up the capability provider itself.
This includes details required for the transport mechanism used to access the capability, such as usernames and passwords for authenticating with the underlying system that provides the capability.
Each capability service may have its own specific set of configurations. As such, check the capability service documentation for details.
These configurations are specific to individual tools that leverage a particular capability. They include:
- Names and identifiers that differentiate tools using the same capability, like specific Kafka topics or the names of database tables.
- Operational properties that dictate how the tool behaves, such as the type of HTTP method (
GET,POST,PUT), or operational settings like timeout configurations and idempotence flags.
These configurations are handled when adding a new tool to Wanaku MCP Router.
Note
Check the "Configuring the Capabilities" section for additional details about this.
The wanaku capabilities list command provides a comprehensive view of all service capabilities available in the Wanaku Router.
It discovers and displays both management tools and resource providers, along with their current operational status and
activity information.
The command combines data from multiple API endpoints to present a unified view of the system's capabilities in an easy-to-read table format.
The command displays the results in a table with the following columns:
| Column | Description |
|---|---|
| service | Name of the service |
| serviceType | Type/category of the service |
| host | Hostname or IP address where the service runs |
| port | Port number the service listens on |
| status | Current operational status (active, inactive, or -) |
| lastSeen | Formatted timestamp of last activity |
For instance, running the command, should present you with an output similar to this:
The wanaku capabilities show command lets you view detailed information for a specific service capability within the
Wanaku MCP Router.
This includes its configuration parameters, current status, and connection information.
wanaku capabilities show <service> [--host <url>]<service>: The service name to show details for (e.g., http, sqs, file)--host <url>: The API host URL (default: http://localhost:8080)
When you execute the command, Wanaku displays comprehensive details about the chosen service type. If multiple instances of the same service exist, an interactive menu will appear, allowing you to select the specific instance you wish to view.
For example, to show the details for the HTTP service:
wanaku capabilities show httpOr, show details for SQS service linked with to a specific Wanaku MCP router running at http://api.example.com:8080:
wanaku capabilities show sqs --host http://api.example.com:8080The command displays two main sections:
- Capability Summary: Basic service information in table format:
- Service name and type
- Host and port
- Current status
- Last seen timestamp
- Configurations: Detailed configuration parameters:
- Parameter names
- Parameter descriptions
When multiple instances of the same service are found, you'll see:
- A warning message indicating multiple matches
- An interactive selection prompt with service details
- Choose your desired instance using arrow keys and Enter
Note
The Wanaku CLI provides clear exit codes to indicate the outcome of a command:
0: The command executed successfully.1: An error occurred (e.g., no capabilities were found, or there were issues connecting to the API).
The MCP bridge in Wanaku allows it to act as a central gateway or proxy to other MCP servers that use HTTP as the transport mechanism.
This feature enables a centralized endpoint for aggregating tools and resources provided by other MCP servers.
To view a list of currently configured forwards, use the wanaku forwards list command:
wanaku forwards listThis command displays information about each forward, including its name, service URL, and any other relevant details.
This can be useful for managing and troubleshooting MCP server integrations.
To add an external MCP server to the Wanaku instance, use the wanaku forwards add command:
wanaku forwards add --service="http://your-mcp-server.com:8080/mcp/sse" --name my-mcp-server--service: The URL of the external MCP server's SSE (Server-Sent Events) endpoint.--name: A unique human-readable name for the forward, used for identification and management purposes.
Once a forward is added, all tools and resources provided by the external MCP server will be mapped in the Wanaku instance.
These tools and resources can then be accessed as if they were local to the server.
To remove a specific external MCP server from the Wanaku instance, use the wanaku forwards remove command:
wanaku forwards remove --name my-mcp-server--name: The human-readable name for the forward to be removed.
Warning
Forward removal operations cannot be undone. Once removed, the tools and resources from those MCP servers will no longer be accessible.
Note
Attempting to remove a non-existent forward will result in an error message.
Suppose you have two MCP servers: http://mcp-server1.com:8080/mcp/sse and http://mcp-server2.com:8080/mcp/sse.
To integrate these external MCP servers into your Wanaku instance, follow these steps:
- Add the first forward using the
wanaku forwards addcommand:
wanaku forwards add --service="http://mcp-server1.com:8080/mcp/sse" --name mcp-server-1- Use the
wanaku forwards listcommand to confirm that the forward has been successfully added:
wanaku forwards list- Verify that all tools and resources from
mcp-server1are now accessible within your Wanaku instance usingwanaku tools list
Name Type URI
tavily-search-local => tavily => tavily://search?maxResults={parameter.value('maxResults')}
meow-facts => mcp-remote-tool => <remote>
dog-facts => mcp-remote-tool => <remote>
camel-rider-quote-generator => mcp-remote-tool => <remote>
tavily-search => mcp-remote-tool => <remote>
laptop-order => mcp-remote-tool => <remote>- Add the second forward using the same command:
wanaku forwards add --service="http://mcp-server2.com:8080/mcp/sse" --name mcp-server-2- Confirm that tools and resources from both external MCP servers are now integrated into your Wanaku instance (use
wanaku tools list) - Use the
wanaku forwards listcommand to view the updated list of forwards:
wanaku forwards listBy leveraging the MCP bridge feature, you can create a centralized endpoint for aggregating tools and resources from multiple external MCP servers, simplifying management and increasing the overall functionality of your Wanaku instance.
Wanaku introduces the concept of namespaces to help users organize and isolate tools and resources, effectively managing the Large Language Model (LLM) context. This prevents context bloat and improves the efficiency of your Wanaku deployments.
Namespaces provide a mechanism to group related tools and resources.
Each namespace acts as a separate logical container, ensuring that the LLM context for tools within one namespace does not interfere with tools in another. This is particularly useful when you have a large number of tools or when different sets of tools are used for distinct purposes.
Wanaku provides a fixed set of 10 available slots for namespaces, named from ns-0 to ns-9.
It also provides a default namespace,
which is used if none is specified and a special public namespace that can be accessed without any authentication.
To associate a tool or resource with a specific namespace, use the --namespace option when adding it:
wanaku tools add -n "meow-facts-3" --description "Retrieve random facts about cats" --uri "https://meowfacts.herokuapp.com?count={count or 1}" --type http --property "count:int,The count of facts to retrieve" --namespace test --required countIn the example above, the meow-facts-3 tool will be associated with the first freely available namespace.
When you provide a namespace name like test, Wanaku automatically associates it with an available numerical slot from ns-0
to ns-9.
You can verify which namespace a tool or resource has been assigned to by using the wanaku namespaces list command.
This command will display a list of all active namespaces, their unique IDs, and their corresponding paths.
The output will look similar to this:
id name path
28560e66-d94c-44a2-b032-779b5542132a http://localhost:8080/ns-4/mcp/sse
43b5d7a7-4e7d-4109-960b-ac7695b6f2d3 public http://localhost:8080/public/mcp/sse
93c5bfdf-0e09-4da5-82fa-4eec3bf6b1b4 http://localhost:8080/ns-3/mcp/sse
bfd112d2-32cb-475a-9f55-63301519152b http://localhost:8080/ns-7/mcp/sse
f5915650-4daa-4616-95c6-5aafceffb026 http://localhost:8080/ns-1/mcp/sse
db89fedd-ffe6-4dee-b051-bcd5285bb9c9 http://localhost:8080/ns-2/mcp/sse
d4249e11-9368-4c5b-bb66-981d2d2e69c7 http://localhost:8080/ns-0/mcp/sse
8898fab6-3774-427f-8400-8c6f6fd9a97e http://localhost:8080/ns-6/mcp/sse
fe8cc1f2-2355-4009-ba68-4faeefe937f7 http://localhost:8080/ns-5/mcp/sse
a3dfaaf6-3655-4bcc-8c48-3d183b6d675b http://localhost:8080/ns-8/mcp/sse
8832e2c7-3bd9-4f9b-88ba-982cc20a43de http://localhost:8080/ns-9/mcp/sse
<default> http://localhost:8080//mcp/sseIn this output, you can see the mapping of internal namespace IDs to their corresponding ns-X paths.
Important
For Streamable HTTP, remove the /sse from the path (i.e.: http://localhost:8080/ns-1/mcp/).
If you do not specify a namespace when adding a tool or resource, it will automatically be added to the default namespace.
The default namespace acts as a general container for tools that don't require specific isolation.
You can identify the default namespace in the wanaku namespaces list output by its <default> name.
Labels provide a flexible way to organize and filter namespaces. You can add metadata to namespaces in the form of key-value pairs, making it easier to manage and query them.
You can add labels to an existing namespace using the wanaku namespaces label add command.
To specify which namespace to add labels to, you need the namespace ID from the wanaku namespaces list output (the first column):
# Add a single label to a namespace
wanaku namespaces label add --id 28560e66-d94c-44a2-b032-779b5542132a --label env=production
# Add multiple labels at once
wanaku namespaces label add --id 28560e66-d94c-44a2-b032-779b5542132a -l env=production -l tier=backend -l version=2.0If a label key already exists, its value will be updated to the new value.
You can add labels to multiple namespaces at once using label expressions:
# Add a label to all namespaces matching a label expression
wanaku namespaces label add --label-expression 'category=internal' --label migrated=true
# Add multiple labels to namespaces matching complex expressions
wanaku namespaces label add -e 'env=staging & tier=backend' -l reviewed=true -l compliant=yesTo remove labels from a namespace, use the wanaku namespaces label remove command:
# Remove a single label from a namespace
wanaku namespaces label remove --id 28560e66-d94c-44a2-b032-779b5542132a --label env
# Remove multiple labels at once
wanaku namespaces label remove --id 28560e66-d94c-44a2-b032-779b5542132a -l env -l tier -l versionSimilar to adding labels, you can remove labels from multiple namespaces using label expressions:
# Remove labels from all namespaces matching an expression
wanaku namespaces label remove --label-expression 'category=temp' --label temp
# Remove multiple labels from matching namespaces
wanaku namespaces label remove -e 'migrated=true' -l temp -l draftYou can filter namespaces by their labels when listing them:
# List all namespaces with a specific label
wanaku namespaces list --label-filter 'env=production'
# List namespaces matching complex expressions
wanaku namespaces list --label-filter 'env=production & tier=backend'See the Label Expressions Guide for detailed information on the label expression syntax and advanced filtering options.
Wanaku provides shell completion support for bash and zsh, enabling tab-completion for all commands, subcommands, and their options. This significantly improves the command-line experience by reducing typing and helping discover available commands and options.
To generate a completion script, use the wanaku completion generate command:
# Generate completion script and output to stdout
wanaku completion generate
# Save completion script to a file
wanaku completion generate --output ~/.wanaku_completionThe generated script includes completion support for:
- All parent commands (namespaces, tools, resources, forwards, capabilities, etc.)
- All subcommands (namespaces label add, tools list, etc.)
- All command options (--help, --verbose, --plain, command-specific options)
- Automatic detection of bash vs zsh shell
If you want to enable completion for just your current terminal session without making permanent changes:
# One-liner for bash or zsh (works on both Linux and macOS)
source <(wanaku completion generate)
# Alternative using eval (also works on both bash and zsh)
eval "$(wanaku completion generate)"This generates and immediately sources the completion script in your current shell. Completion will be active until you close the terminal, without creating any files or modifying your shell configuration files.
This is useful for:
- Testing completion before permanent installation
- Temporary/one-time use
- Environments where you don't want to modify shell configuration
- Generate the completion script to a standard location:
wanaku completion generate --output /etc/bash_completion.d/wanaku_completion- Add the following line to your
~/.bashrc:
source /etc/bash_completion.d/wanaku_completion- Reload your shell:
source ~/.bashrcAlternatively, for user-specific installation:
wanaku completion generate --output ~/.wanaku_completion
echo "source ~/.wanaku_completion" >> ~/.bashrc
source ~/.bashrc- Generate the completion script:
mkdir -p ~/.zsh/completions
wanaku completion generate --output ~/.zsh/completions/_wanaku- Add the following lines to your
~/.zshrc:
autoload -U +X bashcompinit && bashcompinit
source ~/.zsh/completions/_wanaku- Reload your shell:
source ~/.zshrc- Generate the completion script:
mkdir -p ~/.zsh/completions
wanaku completion generate --output ~/.zsh/completions/_wanaku- Add the following lines to your
~/.zshrc:
autoload -U +X bashcompinit && bashcompinit
source ~/.zsh/completions/_wanaku- Reload your shell:
source ~/.zshrc- Generate the completion script:
wanaku completion generate --output /usr/local/etc/bash_completion.d/wanaku- Add the following line to your
~/.bash_profile:
source /usr/local/etc/bash_completion.d/wanaku- Reload your shell:
source ~/.bash_profileOnce installed, you can use tab-completion with the Wanaku CLI:
# Tab-complete commands
wanaku <TAB>
# Shows: capabilities, completion, forwards, man, namespaces, resources, start, tools, toolset
# Tab-complete subcommands
wanaku namespaces <TAB>
# Shows: label, list
# Tab-complete options
wanaku tools add --<TAB>
# Shows: --description, --help, --name, --namespace, --plain, --property, --required, --type, --uri, --verbose
# Tab-complete after partial input
wanaku name<TAB>
# Completes to: wanaku namespacesIf completion doesn't work after installation:
-
Verify the script was sourced: Check that your shell configuration file (
.bashrc,.zshrc, or.bash_profile) contains the source command and was reloaded. -
Check shell detection: The completion script automatically detects whether you're using bash or zsh. Verify you're using a supported shell:
echo $BASH_VERSION # For bash echo $ZSH_VERSION # For zsh
-
Manually source the script: Try sourcing the completion script directly:
source ~/.wanaku_completion
-
Regenerate the script: If you've updated Wanaku and new commands aren't appearing, regenerate the completion script:
wanaku completion generate --output ~/.wanaku_completion source ~/.wanaku_completion
- PowerShell: Shell completion is not currently supported for PowerShell on Windows. Users on Windows should use WSL (Windows Subsystem for Linux) with bash or zsh for completion support.
- Fish shell: Fish shell is not supported by picocli 4.7.7. Only bash and zsh are supported.
Universal Resource Identifiers (URI) are central to Wanaku.
They are used to define the location of resources, the tool invocation request that Wanaku will receive from the Agent/LLM and the location of configuration and secret properties.
Understanding URIs is critical to leverage Wanaku and create flexible definitions of tools and resources.
Some services may require a more flexible definition of input data.
For instance, consider HTTP endpoints with dynamic parameters:
http://my-host/api/{someId}http://my-host/api/{someId}/createhttp://my-host/api/{someId}/link/to/{anotherId}
In cases where the service cannot predetermine the actual tool addresses, users must define them when creating the tool.
Building the URIs is not always as simple as defining their address. Sometimes, optional parameters need to be filtered out or query parameters need to be built. To help with that, Wanaku comes with a couple of expressions to build them.
To access the values, ou can use the expression {parameter.value('name')}. For instance, to get the value of the parameter id
you would use the expression {parameter.value('id')}. You can also provide default values if none are provided, such as
http://my-host/{parameter.valueOrElse('id', 1)}/data (this would provide the value 1 if the parameter id is not set).
It is also possible to build the query part of URIs with the query method. For instance, to create a URI such as http://my-host/data?id=456
you could use http://my-host/data{parameter.query('id')}. If the id parameter is not provided, this would generate a URI such as
http://my-host/data. This can take multiple parameters, so it is possible to pass extra variables such as
{parameter.query('id', 'name', 'location', ...)}.
Important
Do not provide the ? character.
It is added automatically the parsing code if necessary.
Building the query part of URIs can be quite complex if there are too many. To avoid that, you can use {parameter.query} to build
a query composed of all query parameters.
The values for the queries will be automatically encoded, so a URI defined as http://my-host/{parameter.query('id', 'name')}
would generate http://my-host/?id=456&name=My+Name+With+Spaces if provided with a name value of "My Name With Spaces".
The wanaku_body property is a special argument used to indicate that the associated property or argument should be included in
the body of the data exchange, rather than as a parameter.
For instance, in an HTTP call, wanaku_body specifies that the property should be part of the HTTP body, not the HTTP URI.
The handling of such parameters may vary depending on the service being used.
The wanaku_meta_ prefix is a special argument prefix that allows AI services to inject headers into tool invocations
without requiring changes to the tool's configuration or route definition.
Arguments with this prefix are:
- Extracted from the regular arguments (they are not passed to the tool as arguments)
- Stripped of the
wanaku_meta_prefix - Forwarded as headers in the gRPC tool invocation request
For example, an argument named wanaku_meta_contextId with value ctx-123 becomes a header with key contextId and
value ctx-123.
This is useful for passing context information (such as user IDs, session IDs, or correlation IDs) from the AI service through to the downstream capability service.
@RegisterAiService
public interface MyService {
@McpToolBox("toolbox")
String callTool(
@Header("wanaku_meta_contextId") String contextId,
@Header("wanaku_meta_userId") String userId,
@UserMessage String message
);
}In the tool implementation, these become accessible as headers in the ToolInvokeRequest:
Map<String, String> headers = request.getHeadersMap();
String contextId = headers.get("contextId"); // prefix stripped
String userId = headers.get("userId");Note
If a metadata header has the same name as a tool-defined header (from the tool's schema), the tool-defined header takes precedence.
The wanaku_auth_ prefix is a special argument prefix that allows MCP clients to propagate access tokens or other
credentials to downstream capabilities without exposing them to LLMs.
Arguments with this prefix are:
- Extracted from the regular arguments (they are never passed to LLMs or to the tool as arguments)
- Stripped of the
wanaku_auth_prefix - Forwarded as headers in the gRPC tool invocation request
- Always redacted in logs and observability events
For example, an argument named wanaku_auth_Authorization with value Bearer token-123 becomes a header with key
Authorization and value Bearer token-123.
This is useful for propagating access tokens from MCP clients through to downstream capabilities (HTTP, Camel, etc.) when calling protected third-party APIs.
Unlike wanaku_meta_, authentication arguments have stricter security handling:
- Never exposed to LLMs — filtered from tool arguments before any processing
- Never appear in events — filtered from observability event arguments
- Always redacted in headers — sensitive header names (e.g.,
Authorization) are redacted in event headers - Highest merge priority — auth headers override both metadata and tool-defined headers on conflict
To call a protected third-party API (e.g., GitHub), the MCP client passes the access token via wanaku_auth_:
Arguments from MCP client:
wanaku_auth_Authorization = "Bearer ghp_xxxxxxxxxxxx"
owner = "octocat"
repo = "hello-world"
The wanaku_auth_Authorization argument is extracted and becomes an Authorization header on the outgoing HTTP
request, while owner and repo are passed as regular tool arguments.
Multiple auth tokens can be propagated simultaneously:
Arguments from MCP client:
wanaku_auth_Authorization = "Bearer internal-token"
wanaku_auth_X-Third-Party-Token = "external-token"
Both are extracted and forwarded as separate headers to the downstream capability.
Currently special arguments:
wanaku_body- Indicates the argument should be included in the request bodywanaku_meta_- Prefix for arguments that are converted to headers (e.g.,wanaku_meta_contextId)wanaku_auth_- Prefix for sensitive authentication arguments that are converted to headers with redaction (e.g.,wanaku_auth_Authorization)
Wanaku leverages Quarkus and Apache Camel to provide connectivity to a vast range of services and platforms.
Although we aim to provide a few of them out-of-the box, not all of them will fit all the use cases. For most cases, users should rely on the Camel Integration Capability for Wanaku. That capability service leverages Apache Camel which offers more than 300 components capable of talking to any type of system. Users can design their integrations using tools such as Kaoto or Karavan and expose the routes as tools or resources using that capability service.
For cases where the Camel Integration Capability for Wanaku is not sufficient, users can create their own capability services.
Why try to make it simple for users to create custom services that solve their particular need.
To create a custom resource provider, you can run:
wanaku capabilities create resource --name y4To run the newly created service enter the directory that was created (i.e.,; cd wanaku-provider-y4),
then build the project using Maven (mvn clean package).
Note
Capabilities services are created, by default, using Apache Camel. However, it is possible to create
purely Quarkus-based capabilities using the option --type=quarkus.
Then, launch it using:
java -Dwanaku.service.registration.uri=http://localhost:8080 -Dquarkus.grpc.server.port=9901 ... -jar target/quarkus-app/quarkus-run.jarYou can check if the service was registered correctly using wanaku capabilities list.
Important
Remember to set the parameters in the application.properties file and also adjust the authentication settings.
After created, then most of the work is to adjust the auto-generated Delegate class to provide the Camel-based URI and, if
necessary, coerce (convert) the response from its specific type to String.
To create a custom tool service, you can run:
wanaku capabilities create tool --name jmsNote
Capabilities services are created, by default, using Apache Camel. However, it is possible to create
purely Quarkus-based capabilities using the option --type=quarkus.
To run the newly created service enter the directory that was created (i.e.,; cd wanaku-tool-service-jms), then build the project using Maven (mvn clean package).
Then, launch it using:
java -Dwanaku.service.registration.uri=http://localhost:8080 -Dquarkus.grpc.server.port=9900 ... -jar target/quarkus-app/quarkus-run.jarYou can check if the service was registered correctly using wanaku capabilities list.
Important
Remember to set the parameters in the application.properties file and also adjust the authentication settings.
To customize your service, adjust the delegate and client classes.
After created, then most of the work is to adjust the auto-generated Delegate and Client classes to invoke the service and
provide the returned response.
In those cases, then you also need to write a class that leverages Apache Camel's ProducerTemplate
and (or, sometimes, both) ConsumerTemplate to interact with the system you are implementing connectivity too.
To create a custom mcp server, you can run:
wanaku capabilities create mcp --name s3To run the newly created service enter the directory that was created (i.e.,; cd wanaku-mcp-servers-s3),
then build the project using Maven (mvn clean package).
Note
Capabilities services are created, by default, using Apache Camel. However, it is possible to create
purely Quarkus-based capabilities using the option --type=quarkus.
Then, launch it using:
java -Dwanaku.service.registration.uri=http://localhost:8080 -Dquarkus.grpc.server.port=9901 ... -jar target/quarkus-app/quarkus-run.jarYou can check if the service was registered correctly using wanaku forwards list.
Important
Remember to set the parameters in the application.properties file.
After created, then most of the work is to adjust the auto-generated Tool class to implement the mcp server tool.
The communication between Wanaku MCP Router and its downstream services is capable of talking to any type of service using gRPC. Therefore, it's possible to implement services in any language that supports it.
For those cases, leverage the .proto files in the core-exchange module for creating your own service.
Caution
At this time, Wanaku is being intensively developed, therefore, we cannot guarantee backwards compatibility of the protocol.
Note
For plain Java, you can still generate the project using the archetype, but in this case, you must implement your own delegate from scratch and adjust the dependencies.
You can adjust the address used to announce to the MCP Router using either (depending on whether using a tool or a resource provider):
wanaku.service.registration.announce-address=my-host
This is particularly helpful when running a capability service in the cloud, behind a proxy or firewall.
quarkus.oidc-client.auth-server-url=http://localhost:8543/realms/wanakuquarkus.oidc-client.client-id=wanaku-servicequarkus.oidc-client.refresh-token-time-skew=1mquarkus.oidc-client.credentials.secret=<insert key here>
Wanaku implements the MCP protocol and, by definition, should support any client that is compliant to the protocol.
The details below describe how Wanaku MCP router can be used with some prominent MCP clients:
Wanaku Console includes simple LLMChat specificly designed for quick testing of the tools.
Note
At the moment, the Embedded LLMChat supports only the tools.
open http://localhost:8080- Setup LLM -
baseurl,api key,model, and extra parameters - Select tools
- Enter prompt and send
mvn -B archetype:generate -DarchetypeGroupId=ai.wanaku -DarchetypeArtifactId=wanaku-mcp-servers-archetype \
-DarchetypeVersion=0.0.8 -DgroupId=ai.wanaku -Dpackage=ai.wanaku.mcp.servers.s3 -DartifactId=wanaku-mcp-servers-s3 \
-Dname=S3 -Dwanaku-version=0.0.8 -Dwanaku-capability-type=camelImportant
When using the maven way, please make sure to adjust the version of Wanaku
to be used by correctly setting the wanaku-version property to the base Wanaku version to use.
After creating the mcp server, open the pom.xml file to add the dependencies for your project.
Using the example above, we would include the following dependencies:
<dependency>
<groupId>org.apache.camel.quarkus</groupId>
<artifactId>camel-quarkus-aws-s3</artifactId>
</dependency>Adjust the gPRC port in the application.properties file by adjusting the quarkus.grpc.server.port property.
Note
You can also provide the port when launching
(i.e., java -Dquarkus.grpc.server.port=9190 -jar target/quarkus-app/quarkus-run.jar)
Then, build the project:
mvn clean packageAnd run it:
java -jar target/quarkus-app/quarkus-run.jarTo integrate Wanaku with Claude Desktop, you will need to add an entry into the claude_desktop_config.json file - see instructions for creating a Claude desktop configuration if you do not already have one.
Claude Desktop does not currently support connecting to SSE-based endpoints, so you will have to configure wanaku using a stdio-to-sse wrapper. Note that you will have to install for this purpose, and specify the SSE URL for your Wanaku instance in the arguments.
{
"mcpServers": {
"wanaku": {
"command": "uvx",
"args": [
"mcp-proxy",
"http://localhost:8080/mcp/sse/"
]
}
}
}Wanaku works with HyperChat. To do so, you can configure Wanaku as an MCP server using the MCP configuration as shown below:
Important
Make sure to have Wanaku up and running before configuring HyperChat. You may also need to close and reopen HyperChat.
After configuring HyperChat, you may need to go the Main Window and edit any existing agent if you have any.
Then, in the agent configuration Window, in the allowMCPs option, make sure you mark Wanaku as an allowed MCP server. If in
doubt, check the HyperChat project documentation.
Note
Older versions of HyperChat (pre 1.1.13) required manually editing the mcp.json file as described on the
improvement ticket. This is not necessary
for newer versions.
For LibreChat search for mcpServers on the librechat.yml file and include something similar to this:
mcpServers:
everything:
url: http://host.docker.internal:8080/mcp/sse
Important
Make sure to point to the correct address of your Wanaku MCP instance.
In LibreChat, you can access Wanaku MCP tools using Agents.
We also have tested Wanaku with Witsy - AI Desktop Assistant.
Wanaku does not support stdio. Therefore, to use Wanaku with to use it with tools that don't support SSE, it is necessary to use an stdio-to-SSE gateway. The application super gateway can be used for this.
npx -y supergateway --sse http://localhost:8080/mcp/sse
Visit this page to check all the providers that come built-in with Wanaku.
Note
Most users should rely on the Camel Integration Capability for Wanaku.
Visit this page to check all the tools that come built-in with Wanaku.
Note
Most users should rely on the Camel Integration Capability for Wanaku.
All CLI commands use the Wanaku management API under the hood. If you need more advanced functionality or want to automate tasks, you may be able to use this API directly.
By using these CLI commands, you can manage resources and tools for your Wanaku MCP Router instance.
This section provides solutions to common issues you may encounter while using Wanaku.
Symptoms:
- CLI commands fail with authentication errors
- Web UI redirects to Keycloak but login fails
Solutions:
-
Verify Keycloak is running and accessible:
curl http://localhost:8543/health
-
Check that the Keycloak realm is properly configured:
- Ensure the
wanakurealm exists - Verify the
wanaku-mcp-routerclient is configured - Confirm user accounts have been created
- Ensure the
-
Clear stored credentials and re-authenticate:
rm ~/.wanaku/credentials wanaku auth login --url http://localhost:8080 -
Verify the router can reach Keycloak:
- Check the
auth.serverconfiguration property - Ensure network connectivity between components
- Check the
Symptoms:
- Commands work initially but fail after some time
- Error messages about expired tokens
Solutions:
-
Re-authenticate with the router:
wanaku auth login --url http://localhost:8080
-
Check token lifetime settings in Keycloak if tokens expire too quickly
Symptoms:
- Services start successfully but don't show up in
wanaku capabilities list - Tools or resources from a service are not available
Solutions:
-
Verify the service registration configuration:
# In the capability service application.properties wanaku.service.registration.enabled=true wanaku.service.registration.uri=http://localhost:8080 -
Check service logs for registration errors:
# Look for registration-related errors grep -i "registration" /path/to/service.log
-
Verify network connectivity between the service and router:
# From the service host curl http://localhost:8080/q/health -
Check if the service is using the correct OIDC credentials:
- Verify
quarkus.oidc-client.credentials.secretmatches the secret in Keycloak - Ensure the
wanaku-serviceclient exists in Keycloak
- Verify
-
Check the router backend logs for incoming registration requests
Symptoms:
- Service appears in
wanaku capabilities listbut marked as offline - Intermittent availability
Solutions:
-
Verify the service is running:
# Check if the gRPC port is listening netstat -an | grep 9009
-
Check the registration interval and ensure heartbeats are being sent:
# In application.properties wanaku.service.registration.interval=10s -
Review service health and ensure it's not crashing or restarting
Symptoms:
- MCP clients fail to connect
- Timeout errors when connecting
Solutions:
-
Verify the router is running and accessible:
curl http://localhost:8080/q/health
-
Check the correct MCP endpoint is being used:
- SSE transport:
http://localhost:8080/mcp/sse - Streamable HTTP:
http://localhost:8080/mcp/
- SSE transport:
-
For namespace-specific connections, ensure the correct path:
# For namespace ns-1 http://localhost:8080/ns-1/mcp/sse -
Verify firewall rules allow traffic on port 8080
-
Check CORS settings if connecting from a web application:
quarkus.http.cors.enabled=true quarkus.http.cors.origins=http://localhost:3000
Symptoms:
wanaku tools listshows tools, but they don't appear in the MCP client- Resources are registered but not accessible
Solutions:
-
Verify the tool/resource is in the correct namespace:
wanaku tools list wanaku namespaces list
-
Check if the client is connected to the correct namespace endpoint
-
Refresh the MCP client connection
-
Verify the capability service providing the tool is online:
wanaku capabilities list
Symptoms:
- Tool appears in client but execution fails
- Error messages when calling a tool
Solutions:
-
Check the tool URI is correct:
wanaku tools list
-
Verify the capability service is running and healthy
-
Review capability service logs for errors during tool execution
-
Ensure required configuration or secrets are properly set:
wanaku tools list
-
For HTTP tools, verify the target endpoint is accessible from the service
Symptoms:
- Resource appears but cannot be read
- Empty or error responses when accessing resources
Solutions:
-
Verify the resource URI and that the target exists:
wanaku resources list
-
Check file permissions if using file-based resources
-
Verify network access if using remote resources (S3, FTP, etc.)
-
Review provider service logs for errors
Symptoms:
- Maven build errors
- Missing artifact errors
Solutions:
-
Ensure you're using the correct Maven version:
mvn --version # Should be 3.x -
Clear Maven cache and rebuild:
rm -rf ~/.m2/repository/ai/wanaku mvn clean install -
Verify internet connectivity for downloading dependencies
Symptoms:
- Native compilation errors
- GraalVM-related failures
Solutions:
-
Verify GraalVM is properly installed:
java -version # Should show GraalVM native-image --version -
Check the Quarkus native build guide for system requirements
-
Try building without native mode first to isolate the issue:
mvn clean package
Symptoms:
- Pods in CrashLoopBackOff state
- ImagePullBackOff errors
Solutions:
-
Verify the container image exists and is accessible:
podman pull quay.io/wanaku/wanaku-router-backend:latest
-
Check pod logs for startup errors:
oc logs <pod-name> kubectl logs <pod-name>
-
Verify ConfigMaps and Secrets are properly mounted:
oc describe pod <pod-name>
-
Check resource limits and ensure sufficient memory/CPU
-
Verify Keycloak is accessible from the pods:
oc exec <pod-name> -- curl http://keycloak:8080/health
Symptoms:
- Tools take a long time to execute
- Resource reads are slow
- MCP clients experience timeouts
Solutions:
-
Check router and service resource usage:
top htop
-
Review logs for errors or warnings
-
Verify network latency between components:
ping <service-host>
-
Check Infinispan cache performance and consider adjusting:
wanaku.infinispan.max-state-count=10
-
For Kubernetes deployments, ensure adequate resource limits:
resources: requests: memory: "512Mi" cpu: "500m" limits: memory: "1Gi" cpu: "1000m"
To get more detailed logs for troubleshooting:
Router backend:
quarkus.log.level=DEBUG
quarkus.log.category."ai.wanaku".level=DEBUG
quarkus.mcp.server.traffic-logging.enabled=trueCapability services:
quarkus.log.level=DEBUG
quarkus.log.category."ai.wanaku".level=DEBUGCLI:
wanaku --verbose tools listTo produce clean, parsable output without ANSI colors or escape sequences (useful for scripting and piping):
wanaku tools list --plainCheck logs in these locations:
- Router backend: Look for
wanaku-router-backend.logor check container logs - Capability services: Check individual service log files
- Kubernetes:
oc logs <pod-name>orkubectl logs <pod-name>
If you continue to experience issues:
- Check the GitHub Issues for similar problems
- Review the documentation
- Join the community discussions
- Open a new issue with:
- Wanaku version
- Deployment environment (local, OpenShift, etc.)
- Steps to reproduce
- Relevant log excerpts
- Configuration (with secrets redacted)